There are two elements every IP address consists of: one element represents the network address, and the other one represents the host address. There is a ‘tool’ (that is a number) called a subnet mask that specifies which part of an IP address to use in order to define the network ID.

Subnetting
A subnet mask divides the IP address into the network address— ‘masking’ or hiding it — and host address. The host part then can be divided into a subnetwork (or a subnet), and host address, in case there is a need for additional subnetwork to boost performance and security of the network.
Systems that are in the same subnet are able to interact directly with each other without additional permission or equipment, while different subnet systems can’t communicate directly — they have to interact via a router. Therefore, subnets are also essential for separating multiple networks and restricting the traffic between them.
How it works
Let’s have a look at an IPv4 subnet mask. It consists of four bytes (32 bits) and is written the same way as an IP address of this version — a string of groups of decimal numbers each separated by a full stop. A subnet mask works by setting all the bits of the network to 1s and all the bits of the host to 0s. This transformation allows router not to handle the whole 32-bit address but to look only at the bits chosen by the mask, translating the sequences of eight binary 1s to 255.
The way it looks
There are several network classes such as Class A, B, and C, usually consisting of 8-, 16-, and 24-bits correspondingly, which use slightly different subnet masks. For instance, 255.255.255.0 is the subnet mask commonly used for Class C IP addresses.
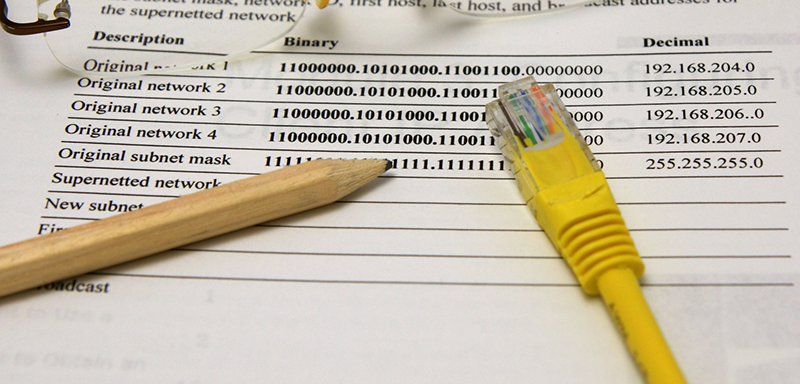
When a subnet mask is applied to an IP address, a bitwise logical AND operation is performed, and as a result, the network address is produced. Let’s take 216.4.128.13 IP address and apply a subnet mask to it:
- IP address: 1101 1000 . 0000 0011 . 1000 0000 . 0000 1100 (216.004.128.013)
- Subnet mask: 1111 1111 . 1111 1111 . 1111 1111 . 0000 0000 (255.255.255.000)
- Network address: 1101 1000 . 0000 0011 . 1000 0000 . 0000 0000 (216.004.128.000)
With the help of subnet masks, organizations can subdivide public IP address blocks to get more IP addresses required for ensuring efficient work process, while they don’t have to get new IP network numbers from an Internet Service Provider (ISP).

